Software projects face supply chain security risk due to insecure artifact downloads via GitHub Actions | CSO Online
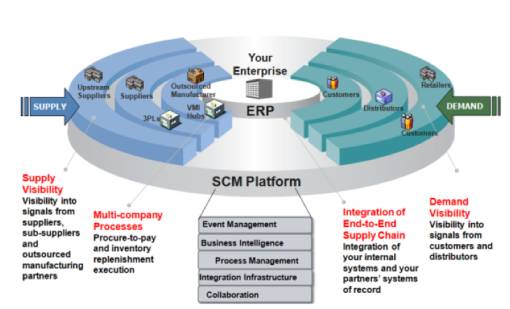
New Software Helps to Mitigate Supply Chain Management Risk > National Security Agency/Central Security Service > Article
Upcoming Strategy to Outline Agency's Supply Chain Security Approach > U.S. Department of Defense > Defense Department News



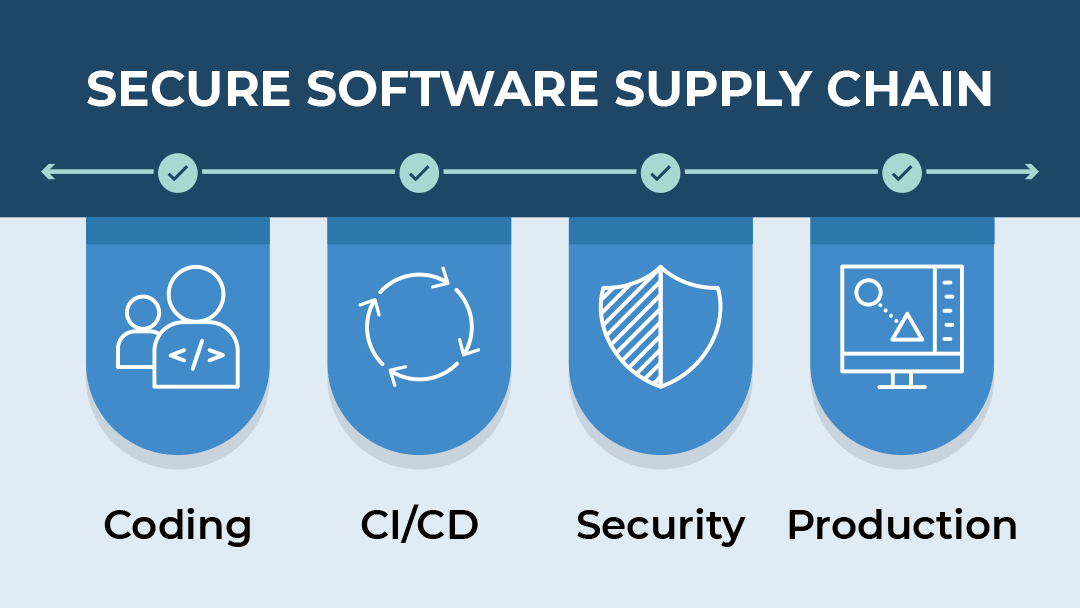






![A Practical Guide to Software Supply Chain Security [10 Tips] - Hashed Out by The SSL Store™ A Practical Guide to Software Supply Chain Security [10 Tips] - Hashed Out by The SSL Store™](https://www.thesslstore.com/blog/wp-content/uploads/2022/12/secure-software-supply-chain-feature.jpg)